Technology
Because soon our backpacks won’t carry anything but video messages, this is a clip from Yihong Technology demonstrating their persistence of vision backpack, that uses a spinning 4-rotor fan with 510 rapidly blinking LEDs to display video. In this case, everyone’s favorite plumber, Mario. WHY he’s everyone’s favorite plumber is
hite
- September 15, 2023
This is a video of Heath Ledger’s Joker performance in The Dark Knight deepfaked by Youtuber GdaTyler VFX to be a makeup-free Heath Ledger. It’s kind of like a reverse deepfake. A FAKEDEEP. Did I just come up with something?! “No.” I didn’t think so, but I can never tell.
hite
- August 1, 2023
This is a painful to watch video of an AI-powered Ameca robotic bust from Engineered Arts using a custom Chat GPT 3 model to attempt to tell a joke. It does an absolutely horrible job, and just gets stuck in some sort of progressive 2 + 2 addition loop. Math
hite
- June 28, 2023
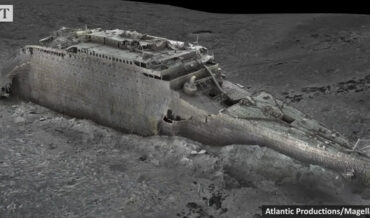
In other cruise ship news, this is a full 3D scan of the Titanic, created using over 700,000 individual stills of the wreckage, where it’s rested in its watery grave some 2+ miles deep in the Atlantic Ocean since 1912. The scan is the largest deep-water 3D project to date,
hite
- May 19, 2023
This is a video highlighting the latest interation of the Tesla Bot, a 5’8″, 125-pound humanoid robot developed by the electric car giant. The robots are powered by the same AI as the driver assistance programming found in Tesla vehicles. Currently, the bots are capable of roaming untethered to explore
hite
- May 17, 2023
Because who hasn’t dreamed of dying inside a giant tire with three of their friends, this is a video from Hunter Goodrich, who made a steel frame and harnesses to fit inside a giant 7-foot tire so four of his friends could ride inside it down a hill. This is
hite
- May 9, 2023
This is a video of mad engineer Shane of Youtube channel Stuff Made Here (previously) attaching a chainsaw to an industrial robotic arm and programming it to carve a dog sculpture out of a block of foam. Its first effort is an absolute disaster, but the second dog it produces
hite
- April 24, 2023
This is a chart detailing averages of how long it would take a modern hacker to brute force passwords of various lengths and complexity using hashed password hacking techniques. If you’re unfamiliar with hashed passwords and how they’re cracked, you can read all about the methodology used HERE. Based on
hite
- April 19, 2023
Things people say
- scoobydoo on Compilation Of Children Running Into Funhouse Mirrors
- 1-Ton on Timelapse Of Walton Goggins Having His Ghoul Face Applied For Fallout
- Eric Ord on Find The Frog
- Kent on Maserati SUV Driver Mistakes His Vehicle For Functional Off Roader, Gets Stuck In Flood
- born in space on Mouse Sneaks Out Of Hiding Spot In Stove To Steal An OREO
- April 19, 2024